CCNA 2 v5.0 Exam Answers
Napjainkban nincs jelentős különbség az asztali és laptop számítógépekben használt alaplapok formai tényezője között.
Valakinek megvannak CISCO IT ESSENTIAL 5. 0 válaszai? (bővebben lent)
CISCO IT ESSENTIAL 5.0-ás verziójából fogok vizsgázni, és a tanár azt mondta, hogy fent vannak a neten a válaszok. De aztán kiderült, hogy az a 4.0-ás válaszai. Kicsit aggasztó, hogy elolvasni az anyagot több mint másfél óra, ráadásul nem is olyan egyszerűek a kérdések, és 80%-ot kell elérni. Egyenlőre csak az első fejezet válaszai érdekelnének, ha valakinek megvan, legyen szíves elküldeni. Előre is köszönöm.
1/2 anonim válasza:
Ezen az oldalon megtalálhatod, bár csak angol nyelven: [link]
U.I: Ez nem neked szól (ahogy elnézem, a téma már nem aktuális), hanem azoknak, akik ugyanazon a kérdés miatt idetántorognak.
CCNA 2 Routing and Switching Essentials (v.5.0) Exam Answers 2014
Routing and Switching Essentials : Describes the architecture, components, and operations of routers and switches in a small network. Students learn how to configure a router and a switch for basic functionality. By the end of this course, students will be able to configure and troubleshoot routers and switches and resolve common issues with RIPv1, RIPv2, single-area and multi-area OSPF, virtual LANs, and inter-VLAN routing in both IPv4 and IPv6 networks.
cisco ccna 5. fejezet vizsga megoldások
cisco ccna 5. fejezet vizsga megoldások.A multimedia demonstration of configuring dynamic NAT on a router is included in the companion digital resource to this book.22.3.2 Configuring PATThe previous example demonstrated the configuration of dynamic NAT; this section describes how to configure PAT on a routeroPAT configuration is much like dynamic NAT and also requires three basic translation commands. First, you need to specify which internal devices’ source addresses are to be converted, using the same commands as dynamic NAT, but you need to specify that PAT is to be performed using the parameter overload.Router(config)# ip nat inside source list standard_IP_ACL_^ pool NAT_pool_name overloadNext, specify the global address pool to be used. Again, the same commands are used as for dynamic NAT.Router(config)# ip nat pool NAT_pool_name beginning_inside_global_IP_address ending_inside ide_global_IP_address netmask subnet_mask_of_ addressesMultiple addresses can be specified in the PAT using the start and end addresses, or just one IP address. Finally, the commands ip nat inside and ip nat outside must be used to tell IOS which interfaces are internal and which are external.The following example in Figure 22.3 shows how to configure the PAT. in this example, 200.200.200.1 is used for static translation of the internal server. In the address pool, only one other IP address (200.200.200.2) is included, and the PAT is performed for only two devices: 192.168.1.10 and 192.168.1.llo configured as follows.Router(config)# ip nat inside source list 1 pool nat-pool overload Router(config)# access-list 1 permit host 192.168.1.10Router(config)# access-list 1 permit host 192.168.1.11 ip nat pool nat-pool 200.200.200.2 200.200.200.2
Free Real CCNA 200-301 Dumps Questions
Refer to the exhibit,which command configures a floating static route to provide a backup to the primary link?
A. ip route 209.165.201.0 255.255.255.224 209.165.202.130
B. ip route 0.0.0.0 0.0.0.0 209.165.200.224
C. ip route 209.165.200.224 255.255.255.224 209.165.202.129 254
D. ip route 0.0.0.0 0.0.0.0 209.165.202.131
Correct Answer: C
What is the primary function of a Layer 3 device?
A. to analyze traffic and drop unauthorized traffic from the Internet
B. to transmit wireless traffic between hosts
C. to pass traffic between different networks
D. forward traffic within the same broadcast domain
Correct Answer: C
An engineer requires a scratch interface to actively attempt to establish a trunk link with a neighbor switch. What command must be configured?
A. switchport mode trunk
B. switchport mode dynamic desirable
C. switchport mode dynamic auto
D. switchport nonegotiate
Correct Answer: B
What is a function of TFTP in network operations?
A. transfers a backup configuration file from a server to a switch using a username and password
B. transfers files between file systems on a router
C. transfers a configuration files from a server to a router on a congested link
cisco ccna 5. fejezet vizsga megoldások
3.4.3 End-to-end encryption 5.5.1 Develop a security strategy (7) Select “Configure manual scanning”, select “Recommended” in “Protection level”, and select “Perform recommended action” in “Action taken by infected object detected”. 5) Step 5 : Find the vulnerability of this machine (1) The basic composition and functions of the Cisco PIX 515 firewall. Web server construction based on SSL protocol Corresponding entity denies that the act has occurred 3) Long jump buffers (Longimpbuffers) (1) The virus spreads through Microsoft’s latest RPC vulnerability, so users should apply the RPC patch to the system first . (2) Identity authentication. Identity authentication emphasizes consistency verification, which must match the consistency proof. Generally, identity authentication includes verification basis, verification system and security requirements. 6.2.1 Characteristics of computer viruses Different types of viruses have their own different characteristics, some of them to the infected file based, some with infected systems lead guide area-based. Most viruses are just a small joke, but a few viruses are extremely harmful ( such as the notorious CIH virus ) , which requires us to use appropriate methods to classify viruses to further meet the needs of daily operations. (1) the % Windows% \ Web \ Folder.htt saved to the % Windows% \ SYSTEM32 \ Setup.txt , the % Win TCP 3. Support the Internet Traditional process encryption method (3) Spread through the Internet. With the rapid development of the Internet, computer viruses have also embarked on the road of high-speed transmission. Now spreading through the Internet has become the first way of spreading computer viruses. High-level data understanding 7.1 Overview of cyber hackers At present, the functional modules in many Trojan horse programs are no longer composed of a single file, but have multiple backups that can be mutually restored. When one of them is deleted, other programs will restore it again, unable to eliminate the roots. (1) G_Server.exe : The background monitoring program of the monitored terminal ( automatically installed after running it once, and can be renamed arbitrarily ) . Before installation, you can perform some special configuration through the local server program function of G_Client , such as whether to send dynamic IP to Specify mailbox, change monitoring port,cisco ccna 5. fejezet vizsga megoldások, set access password, etc. ) . (4) IP segment scanning 1.3.3 Data security issues Table . 5 – 14 Conduit Command Description 4. Non-repudiation Note that the public key encryption and private key decryption mentioned above are information encryption used in the communication field. In sharing software encryption algorithms, we commonly use private key encryption and public key decryption, which is another use of public key algorithms -data (2) The international nature of the network means that network attacks not only come from users of the local network, but also from the Internet 3) Array boundary check Run IE , execute the “Tools” → ” Internet Options ” command, open the “Security” tab in the pop-up dialog box, click the “Custom Level” button, and change the security level from “Medium” to “High”. An Internet worm is an independent program that can run without the intervention of computer users. It spreads by continuously gaining some or all of the control rights on the vulnerable computers in the network. The biggest difference between a worm and an ordinary virus is that it does not require human intervention, and can replicate and spread autonomously and continuously. 4) Unmodifiable information (1) Send yourself out via E-mail . Group number: 12 . 7. Root certificate Encryption (the encrypt) , decryption (the decrypt) : in some way to hide masquerade process it is referred to the original encryption; phase inverse process is called decryption. 1) Destructive Trojan Horse The following first introduces several commonly used network commands and introduces the principle of port scanning. (4) Restart the computer immediately after killing the virus. 2. Trust chain and blacklist issuance When the trusted computing base of the computer information system is initially implemented, the user is first required to identify his own identity, and a protection mechanism ( such as a password ) is used to authenticate the user’s identity; unauthorized users are prevented from accessing user identity authentication data. By providing users with a unique identification, the trusted computing base of computer information systems can make users responsible for their actions. The trusted base of the computer information system also has the ability to associate the identity with all auditable behaviors of the user.
Latest Cisco CCNA 200-301 Dumps
If you want to pass the first exam successfully, the next you must take a serious look! All of our dumps are verified by IT certified experts. Our Latest Cisco CCNA 200-301 Dumps contains all the real topics of the day. What is our goal? To help you pass the exam successfully! You can trust us completely, and we will definitely not let you down. You can find us at anytime because we are willing to serve you guys !
Come on! Do your wisely decision!

Latest Cisco CCNA 200-301 Exam Information
( 16 People are currently looking at this product )
Exam Code: 200-301
Certification Provider: Cisco
Certification Exam Name:Cisco CCNA
Update Date: Oct 05,2022
No service time limit
Our only criterion is to ensure that you pass the exam.
No matter when you go to the exam, we will serve you the day until you go to the exam.
Hope you pass the exam successfully!
100% Pass Exam
We guarantee that you can pass the exam successfully. If the test encounters a change, it will lead to disqualification.
You can continue the service time free of charge by giving us the information that failed the test on the day.
100% Accurate Questions
All the information is up-to-date. We will update and remind you all the latest news.
Pass the least time
According to the survey, have 96% of students pass the exam during 5 days successfully.
Shipped within 24 hours
All dumps are sent by mail. After we confirm your payment,you will receive dumps within 24 hours. If not, please contact us
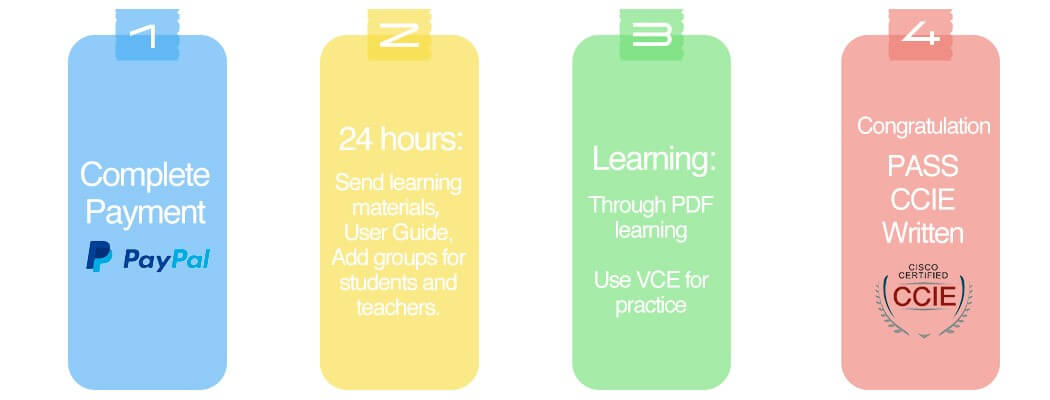
Four Steps to Prepare & Pass Cisco CCNA 200-301 Exam
Step 1: Complete the corresponding written exam fee through PayPal.
Step 2: PASSHOT staff will send the appropriate dumps information to your reserved mailbox within 24 hours.
Step 3: Take the time to study. In general, 96% of students can complete all the study in a week.
Step 4: Pass the Cisco written exam!
How often do you update your study materials?
We update in accord with the vendors if they change the question, our professional team will update our question and answer in a week.
Do I have to pay for the updated information?
Questions outdate of our service period and you will get special discounts.
After order successfully, how can I get learning materials?
All dumps are sent by e-mail. You will receive the dumps or workbooks during 24 hours after we confirm your payment. If not, please contact us.
How do I pay for my order?
PASSHOT supports PayPal and Western Union payments to protect your information and transaction security. If you don’t have PayPal, you can bind your credit card via PayPal.
PayPal currently accepts the following cards: Visa/Mastercard/American Express/PayPal Top Up Card
Can I pass the exam with Q&A only?
Of course! All the question and answers are compiled by experienced experts after in-depth study of real exams and thousands of practice tests. If you understand the knowledge points provided in our Q&A, you can pass the exam.
Why do I choose PASSHOT?
PASSHOT is definitely your first choice for Cisco dumps. Because we have 100% real and effective Cisco dumps. You can definitely pass the exam in a short time with a high score.
Product Reviews * The most recent comment are at the top
these ccna dumps 200-301 make it easier to understand cisco especially since cisco is the toughest certification i can go through
ccna 200-301 premuim file is really valid, i passed!
great sources of information. satisfied with quality that i found. passing was easier from what is given with passhot.
Passhot is updated very quickly, and gave me the latest dumps two days ago which made me pass the exam today. Thank you guys very much.
red lines 2021-04-01
these ccna 200-301 exam questions are easy to manipulate when you have the study guide
Comments are closed, but trackbacks and pingbacks are open.